Large enterprises across KSA and UAE face mounting pressure to manage process risks while maintaining operational efficiency and regulatory compliance. Without a structured process risk management workflow, your organization risks costly failures, compliance penalties, and diminished stakeholder confidence. This guide equips C-level executives and IT decision-makers with a proven framework to implement robust workflows that minimize operational risk, enhance compliance adherence, and drive sustainable enterprise success through systematic risk identification, assessment, mitigation, and continuous monitoring.
Table of Contents
- Key takeaways
- Preparing for an effective process risk management workflow
- Executing the process risk management workflow step-by-step
- Verifying effectiveness and troubleshooting common pitfalls
- Boost your digital transformation with SingleClic
- What is a process risk management workflow?
Key Takeaways
| Point | Details |
|---|---|
| Structured workflow framework | A proven framework helps identify, assess, mitigate, and monitor process risks to improve compliance and resilience. |
| Map critical processes | Start by mapping end to end critical processes and documenting handoffs, decisions, and dependencies to reveal vulnerabilities. |
| Set measurable targets | Define objectives aligned with regional rules and set targets such as reducing violations by 50 percent and cutting incident response time by 60 percent. |
| Assemble cross functional teams | Include IT leaders, risk managers, compliance officers, operations managers, and representatives from finance and legal to capture diverse insights. |
Preparing for an effective process risk management workflow
Successful implementation begins long before you launch your first risk assessment. Your preparation phase determines whether your workflow delivers measurable results or becomes another abandoned initiative. Start by mapping your critical business processes, those that directly impact revenue, customer satisfaction, regulatory compliance, or operational continuity. Document each process end to end, identifying handoffs, decision points, and dependencies that create vulnerability.
Define clear objectives aligned with your enterprise context and regional regulatory landscape. In KSA and UAE, compliance requirements span financial reporting, data protection, industry-specific regulations, and operational standards. Your workflow must address Saudi Arabian Monetary Authority guidelines for financial institutions, UAE Central Bank regulations, or sector-specific frameworks governing healthcare, construction, or telecommunications. Establish measurable targets: reduce compliance violations by 50%, decrease process failure rates by 40%, or cut incident response time by 60%.
Assemble cross-functional teams that bring diverse perspectives to risk identification and mitigation. Your core team should include IT leaders who understand system vulnerabilities, risk managers who assess impact and likelihood, compliance officers who ensure regulatory adherence, and operations managers who know where processes break down. Add representatives from finance, legal, and business units most affected by process risks. This diversity prevents blind spots and ensures your workflow addresses real operational challenges, not theoretical scenarios.
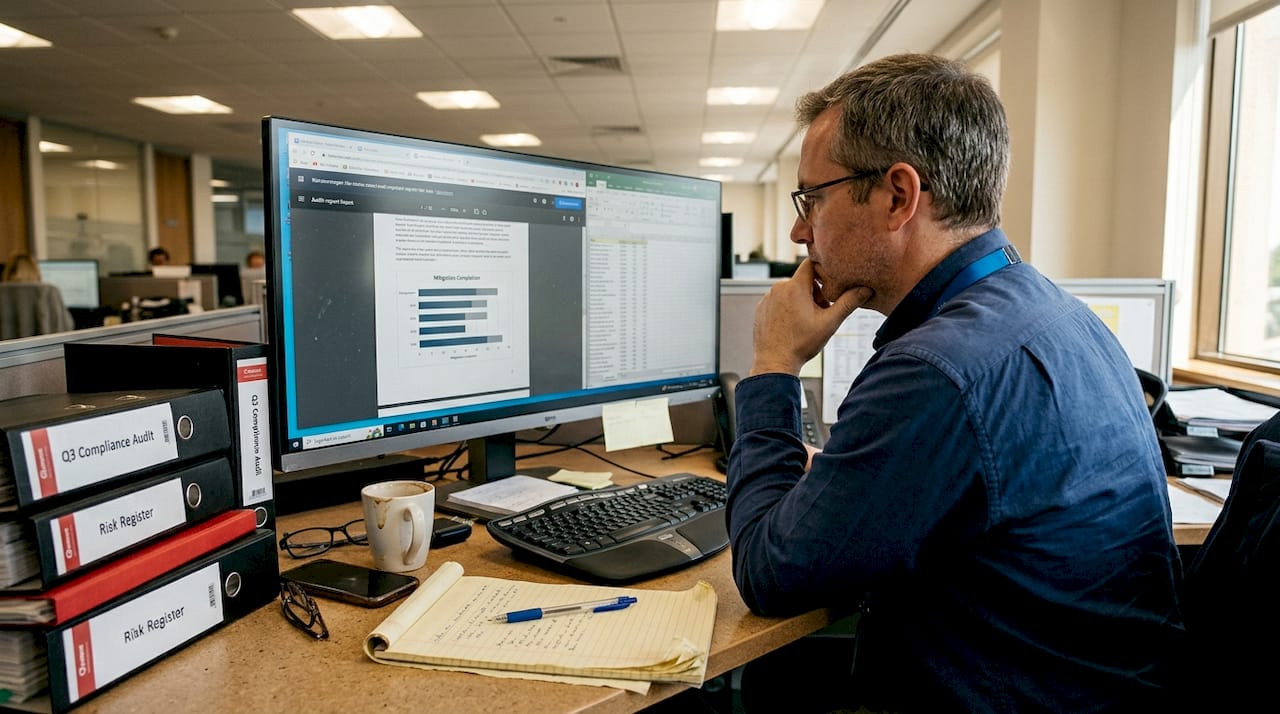
Gather existing documentation that reveals historical patterns and current vulnerabilities. Collect incident reports from the past 24 months, audit findings, compliance violations, customer complaints related to process failures, and performance metrics showing process efficiency. Analyze this data to identify recurring themes: do risks cluster in specific departments, processes, or time periods? Understanding your risk history guides where to focus initial workflow efforts for maximum impact.
Choose digital tools that provide visibility and control throughout your workflow. Successful risk management requires a clear understanding of business processes and risk factors. Your technology stack should support risk register management, assessment scoring, mitigation tracking, real-time monitoring, and compliance reporting. Integration with existing enterprise systems ensures your workflow accesses current data without manual transfers that introduce errors and delays.
Pro Tip: Create a visual process map showing where risks typically emerge in your operations. This single-page reference helps team members quickly identify potential vulnerabilities during daily work, transforming risk awareness from periodic reviews into continuous practice.
| Preparation Element | Team Responsible | Documentation Needed | Tools Required |
|---|---|---|---|
| Process mapping | Operations + IT | Current process flows, system diagrams | Process modeling software |
| Regulatory analysis | Compliance + Legal | Applicable regulations, audit history | Compliance management system |
| Risk history review | Risk + Operations | Incident reports, failure data | Data analytics platform |
| Tool selection | IT + Risk | System requirements, integration needs | Workflow automation platform |
| Team formation | Executive leadership | Stakeholder matrix, RACI chart | Collaboration tools |
With your foundation solidly built, you’re ready to execute the workflow that transforms risk management from reactive firefighting into proactive protection.
Executing the process risk management workflow step-by-step
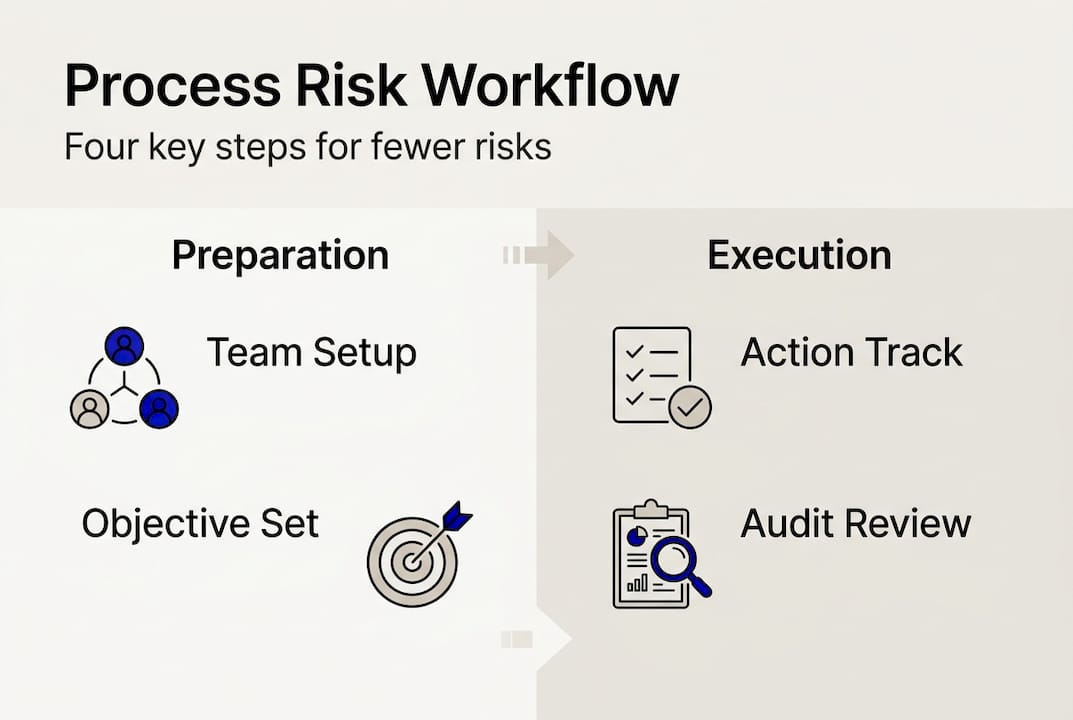
Implementation follows five interconnected phases that create a continuous cycle of risk awareness and mitigation. Each phase builds on the previous one, creating a comprehensive system that catches risks early and responds effectively.
-
Identify and document potential process risks using risk registers. Begin with structured brainstorming sessions where cross-functional teams examine each critical process for potential failure points. Consider operational risks like system outages or supplier failures, compliance risks such as regulatory violations or data breaches, financial risks including fraud or budget overruns, and strategic risks like market changes or competitive threats. Document every identified risk in a centralized register that captures risk description, affected processes, potential triggers, and initial severity estimates. Your risk register becomes the single source of truth that prevents risks from being forgotten or overlooked.
-
Assess risks qualitatively and quantitatively considering impact and likelihood. Evaluate each registered risk across two dimensions: what damage would occur if this risk materialized, and how probable is that occurrence? Use a consistent scoring framework, perhaps a 1-5 scale for both impact and likelihood, then multiply scores to calculate risk priority. High-impact, high-likelihood risks demand immediate attention, while low-impact, low-probability risks may warrant monitoring only. Structured workflows enhance risk detection and mitigation effectiveness. Quantify financial impact where possible: a data breach might cost $2 million in penalties plus reputation damage, while a supplier failure could halt production worth $500,000 daily.
-
Develop and assign mitigation actions with clear owners and timelines. For each high-priority risk, define specific actions that reduce likelihood, minimize impact, or both. Assign a single owner responsible for executing each mitigation action, someone with authority to allocate resources and make decisions. Set realistic deadlines that balance urgency with operational capacity. Mitigation strategies fall into four categories: avoid the risk by changing the process, reduce the risk through controls or redundancy, transfer the risk via insurance or outsourcing, or accept the risk with contingency plans ready.
-
Implement controls and integrate monitoring systems for continuous oversight. Deploy the mitigation actions you’ve designed, embedding controls directly into your processes where possible. Automated controls work better than manual ones: system validations prevent data entry errors more reliably than human review. Establish monitoring mechanisms that alert you when risk indicators spike. If supplier delivery delays represent a risk, track on-time delivery rates weekly and trigger alerts when performance drops below acceptable thresholds. Real-time monitoring transforms your workflow from periodic snapshots into continuous protection.
-
Maintain detailed documentation for compliance and audit readiness. Record every risk identification session, assessment decision, mitigation action, and monitoring result. Documentation serves multiple purposes: it demonstrates due diligence to regulators, provides evidence during audits, enables knowledge transfer when team members change, and creates a learning repository that improves future risk management. Structure documentation so auditors can quickly verify that you identified relevant risks, assessed them appropriately, implemented reasonable mitigations, and monitored results consistently.
Pro Tip: Schedule monthly risk review meetings where teams discuss new risks, reassess existing ones, and verify mitigation progress. This rhythm keeps risk management active in organizational consciousness rather than letting it fade between annual reviews.
Your workflow is now operational, but effectiveness requires ongoing verification and refinement to address emerging challenges.
Verifying effectiveness and troubleshooting common pitfalls
Measuring workflow success requires concrete metrics that reveal whether your risk management efforts actually reduce vulnerabilities and enhance compliance. Track the number of identified risks that materialized versus those successfully prevented, showing your workflow’s protective value. Monitor compliance violation rates before and after workflow implementation, targeting reductions of 50% or more within the first year. Measure incident response time from risk detection to resolution, aiming for continuous improvement as your team gains experience.
Calculate risk mitigation completion rates to ensure assigned actions actually get executed. If only 60% of mitigation actions reach completion, your workflow identifies risks but fails to address them, providing false security. Track audit findings related to risk management processes, expecting fewer observations as your workflow matures. Ongoing verification is essential to ensure compliance and operational efficiency gains. Survey stakeholders quarterly to assess whether they find the workflow valuable or burdensome, adjusting processes based on feedback.
Common pitfalls undermine even well-designed workflows if left unaddressed. Insufficient stakeholder engagement occurs when risk management becomes an isolated function rather than an enterprise-wide responsibility. Combat this by including diverse voices in risk identification, sharing success stories that demonstrate workflow value, and making risk discussions part of regular business reviews. Outdated risk data renders your assessments irrelevant, leading to misallocated resources and missed threats. Establish quarterly risk register reviews where teams verify that documented risks still exist, update likelihood and impact scores based on current conditions, and add newly emerged risks.
Poor documentation creates compliance vulnerabilities and knowledge gaps that weaken your workflow over time. Standardize documentation templates, automate capture where possible, and assign documentation quality checks to ensure completeness. Lack of executive support starves workflows of resources and authority needed for success. Secure leadership commitment by presenting risk management results in business terms: cost avoidance, compliance savings, operational efficiency gains, and reputation protection.
| Common Issue | Symptoms | Recommended Solution |
|---|---|---|
| Insufficient engagement | Low participation in risk sessions, incomplete assessments | Tie risk management to performance reviews, celebrate wins |
| Outdated risk data | Risks that no longer apply, missed emerging threats | Quarterly register reviews, automated data feeds |
| Poor documentation | Missing audit evidence, knowledge loss during transitions | Standardized templates, documentation ownership |
| Weak executive support | Limited resources, low priority status | Regular executive briefings showing business value |
| Manual processes | Slow response times, human errors | Workflow automation for routine tasks |
Implement periodic audits that evaluate workflow adherence and identify improvement opportunities. Internal audits conducted quarterly catch deviations before they become systemic problems, while annual external audits provide independent validation of your approach. Create feedback loops where team members share lessons learned from risk events, both successful mitigations and failures that reveal workflow gaps. This continuous improvement mindset transforms your workflow from a static checklist into a dynamic system that evolves with your enterprise.
Pro Tip: Leverage automation to reduce human errors and accelerate verification. Automated risk scoring, mitigation tracking dashboards, and compliance reporting tools free your team to focus on strategic risk decisions rather than administrative tasks, while improving accuracy and consistency.
With your process risk management workflow verified and refined, consider how partnering with experienced digital transformation experts can amplify your results.
Boost your digital transformation with SingleClic
SingleClic brings over a decade of digital transformation expertise to enterprises across KSA, UAE, and Egypt, helping organizations like yours implement robust process risk management workflows that deliver measurable results. Our team of 70+ consultants and engineers has guided 60+ enterprise clients including Emirates Health Services, QNB, and Emaar Misr through successful digital transformation office initiatives that enhance operational efficiency and compliance adherence.
We specialize in business process management solutions that integrate seamlessly with your existing systems, providing the visibility and control needed for effective risk management. Our proven workflow optimization process frameworks help you move beyond digitalization into true optimization, combining world-class technology with deep industry expertise. Whether you need workflow automation, risk assessment tools, or comprehensive digital transformation guidance, SingleClic delivers scalable solutions tailored to your enterprise context and regulatory requirements.
What is a process risk management workflow?
A process risk management workflow is a structured sequence of activities designed to identify, assess, mitigate, and monitor risks that threaten business processes. It creates a systematic approach where risks are documented in registers, evaluated for impact and likelihood, assigned to owners for mitigation, and tracked through resolution. This workflow transforms risk management from ad hoc reactions into proactive prevention.
The workflow plays a critical role in reducing operational failures by catching vulnerabilities before they cause disruptions. It ensures compliance by embedding regulatory requirements into process design and monitoring adherence continuously. Organizations with mature workflows experience fewer incidents, faster response times, and stronger audit results compared to those relying on informal risk management.
How can C-level executives ensure successful adoption of process risk management?
Leadership must prioritize building a risk-aware culture where every team member understands their role in identifying and mitigating process risks. Allocate sufficient resources including technology, training, and dedicated personnel to support workflow implementation and ongoing operation. Engage cross-functional teams actively by participating in risk reviews, celebrating successful mitigations, and addressing obstacles that prevent effective risk management.
Regularly review key metrics such as risk mitigation completion rates, compliance violation trends, and incident response times to verify that your workflow delivers intended results. Adjust resource allocation, process design, and team structure based on performance data and stakeholder feedback. Executive visibility signals that risk management matters, driving adoption throughout the organization.
What are the common challenges during workflow implementation?
Resistance to change emerges when team members view risk management as additional bureaucracy rather than value-adding protection. Lack of data quality undermines assessments when risk information is incomplete, outdated, or inconsistent across departments. Insufficient stakeholder communication creates confusion about workflow objectives, roles, and expectations, leading to poor participation and incomplete execution.
Address resistance through comprehensive training that demonstrates how the workflow makes jobs easier and protects the organization. Improve data quality by establishing governance standards, automating data collection where possible, and conducting regular validation reviews. Enhance communication through clear documentation, regular updates on workflow progress and wins, and forums where stakeholders can ask questions and share concerns.
Which digital tools best support process risk management workflows?
Workflow automation platforms streamline risk identification, assessment, mitigation tracking, and reporting by eliminating manual handoffs and ensuring consistent process execution. Risk assessment tools provide standardized scoring frameworks, heat maps, and prioritization algorithms that bring objectivity to risk evaluation. Monitoring dashboards deliver real-time visibility into risk indicators, mitigation progress, and compliance status, enabling faster response to emerging threats.
Compliance reporting systems generate audit-ready documentation automatically, reducing preparation time and ensuring completeness. Integration with existing enterprise systems such as ERP, CRM, and operational platforms is essential so your workflow accesses current data without duplicate entry. Choose tools that support your specific regulatory requirements, scale with your enterprise growth, and provide the flexibility to adapt as your risk landscape evolves.









