Protecting sensitive financial and healthcare data in Saudi Arabia and UAE demands a deeper understanding of cybersecurity within modern ERP systems. Organizations face rising threats, including ransomware and social engineering attacks, that can bypass outdated perimeter defenses. By adopting advanced threat detection frameworks powered by artificial intelligence and big data analytics, CIOs and cybersecurity heads can strengthen their ERP security and maintain compliance across dynamic enterprise environments.
Table of Contents
- Defining Cybersecurity in Modern ERP Systems
- Common Threats Targeting ERP Environments
- Healthcare and Banking Compliance Requirements
- Core Components of ERP Security Architecture
- Practical Steps to Avoid System Vulnerabilities
Key Takeaways
| Point | Details |
|---|---|
| Cybersecurity Evolution | Modern ERP systems require advanced cybersecurity strategies that include AI and machine learning for threat detection and prevention. |
| Common Threats | Ransomware, insider threats, and social engineering attacks are prominent risks specifically targeting ERP environments. |
| Compliance Requirements | Healthcare and banking sectors in Saudi Arabia and UAE must comply with strict regulations, requiring comprehensive cybersecurity measures. |
| Proactive Strategies | Organizations should implement regular security assessments and employee training to effectively mitigate vulnerabilities in ERP systems. |
Defining Cybersecurity in Modern ERP Systems
Modern Enterprise Resource Planning (ERP) systems represent complex technological ecosystems requiring sophisticated cybersecurity approaches. These integrated platforms manage critical business processes and sensitive data across multiple organizational functions, making them prime targets for sophisticated cyber attacks. In Saudi Arabia and UAE, where digital transformation is rapidly accelerating, understanding ERP cybersecurity has become paramount for enterprises seeking robust digital resilience.
Cybersecurity in contemporary ERP environments goes far beyond traditional perimeter defense mechanisms. Advanced threat detection frameworks now leverage artificial intelligence and machine learning to proactively identify and neutralize potential security risks. These modern approaches analyze complex data patterns, detecting anomalies that traditional security methods might overlook.
Key cybersecurity components for modern ERP systems include:
Here is a comparison of traditional ERP cybersecurity approaches versus modern, AI-driven methods:
| Approach Type | Detection Speed | Adaptability to Threats | Resource Requirement |
|---|---|---|---|
| Traditional (Perimeter) | Slower, often reactive | Limited to known attacks | High manual involvement |
| AI-Driven (Advanced) | Real-time, proactive | Learns and adapts to new threats | Automated; less manual workload |
- Real-time threat monitoring
- Automated intrusion detection systems
- Advanced authentication protocols
- Continuous vulnerability assessment
- Encrypted data transmission channels
- Granular access control mechanisms
Pro tip: Implement multi-factor authentication and conduct regular cybersecurity training to minimize human-error related vulnerabilities in your ERP ecosystem.
Common Threats Targeting ERP Environments
Enterprise Resource Planning (ERP) systems in Saudi Arabia and UAE face an increasingly complex cybersecurity landscape, with sophisticated attackers constantly developing new strategies to breach organizational defenses. Cyber threat intelligence reports reveal multiple attack vectors that specifically target these critical business platforms, making comprehensive security awareness paramount for protecting sensitive corporate data.

The most prevalent threats targeting ERP environments include sophisticated attack mechanisms designed to exploit system vulnerabilities. Ransomware represents a significant risk, where cybercriminals encrypt critical business data and demand monetary compensation for restoration. Social engineering attacks like phishing remain particularly dangerous, manipulating employees into revealing login credentials or installing malicious software that can compromise entire organizational networks.
Key cybersecurity threats in modern ERP systems encompass multiple sophisticated attack strategies:
- Ransomware infiltration
- Insider threat exploitation
- Advanced persistent threats (APTs)
- Unauthorized data access
- Credential theft
- Supply chain compromises
- Complex malware injection
Pro tip: Implement comprehensive security awareness training and adopt a zero-trust security model to proactively mitigate potential ERP system vulnerabilities.
Healthcare and Banking Compliance Requirements
In Saudi Arabia and UAE, healthcare and banking sectors face stringent regulatory frameworks that demand robust cybersecurity measures for Enterprise Resource Planning (ERP) systems. Healthcare data security represents a critical intersection of technological protection and regulatory compliance, requiring organizations to implement comprehensive safeguards that protect sensitive patient and financial information.
Compliance requirements for these sectors involve multiple layers of regulatory oversight. Financial institutions must adhere to strict data protection standards that mandate encryption, secure access controls, and comprehensive audit trails. Healthcare organizations similarly face complex regulations surrounding patient data privacy, including requirements for anonymization, secure data transmission, and rigorous access management protocols.
Key compliance requirements for healthcare and banking ERP systems include:
The following table summarizes compliance focus areas for healthcare and banking ERP systems in Saudi Arabia and UAE:
| Sector | Primary Compliance Focus | Typical Standard | Main Data at Risk |
|---|---|---|---|
| Healthcare | Patient data confidentiality | HIPAA, local laws | Personal health information |
| Banking | Financial data protection | PCI DSS, GDPR | Account and transaction data |
- HIPAA compliance for healthcare data protection
- Payment Card Industry (PCI) DSS standards
- GDPR data privacy regulations
- Local Saudi Arabian and UAE data protection laws
- Mandatory encryption of sensitive information
- Regular security vulnerability assessments
- Comprehensive access management protocols
- Detailed logging and monitoring systems
Pro tip: Develop a comprehensive compliance roadmap that integrates continuous monitoring, regular staff training, and proactive security assessments to maintain regulatory alignment.
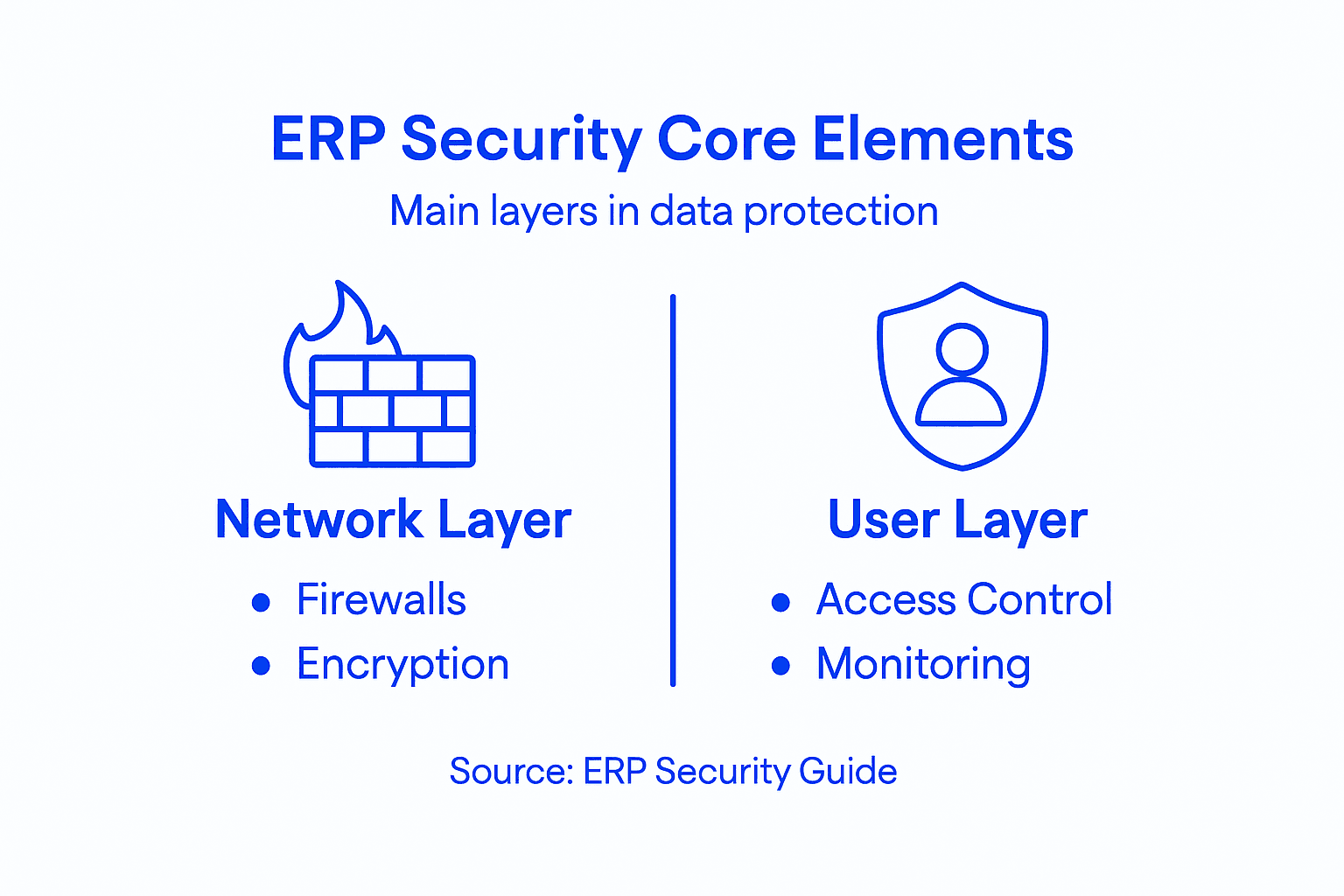
Core Components of ERP Security Architecture
ERP security architecture represents a multilayered defense strategy critical for protecting organizational data across Saudi Arabian and UAE enterprises. SAP ERP security architecture demonstrates the complexity of modern enterprise protection mechanisms, integrating multiple sophisticated components designed to prevent unauthorized access and maintain data integrity.
The core security framework encompasses several interdependent layers that work together to create comprehensive protection. Authentication mechanisms serve as the first line of defense, utilizing advanced techniques like multi-factor authentication, biometric verification, and role-based access controls. Encryption protocols further strengthen security by transforming sensitive data into unreadable formats, ensuring that even if unauthorized access occurs, the information remains protected.
Key components of robust ERP security architecture include:
- Identity and access management systems
- Advanced encryption technologies
- Continuous network monitoring
- Real-time threat detection algorithms
- Secure data transmission protocols
- Comprehensive user activity logging
- Automated vulnerability assessment tools
- Integrated incident response frameworks
Pro tip: Implement a dynamic, adaptive security architecture that combines automated monitoring with regular human-led security audits to maintain comprehensive protection.
Practical Steps to Avoid System Vulnerabilities
In the complex digital landscapes of Saudi Arabia and UAE, organizations must adopt proactive strategies to mitigate ERP system vulnerabilities. Advanced machine learning models have emerged as powerful tools for detecting and preventing potential security breaches, transforming how enterprises approach cybersecurity risk management.
Systematic vulnerability prevention requires a comprehensive, multifaceted approach. Human factors play a critical role, with employee training and awareness being as important as technological safeguards. Technical controls must be implemented strategically, focusing on creating multiple layers of defense that can adapt to evolving cyber threats and organizational changes.
Key practical steps to avoid system vulnerabilities include:
- Conduct regular security vulnerability assessments
- Implement zero-trust security architecture
- Develop comprehensive employee cybersecurity training programs
- Maintain rigorous patch management protocols
- Enable advanced multi-factor authentication
- Deploy continuous network monitoring systems
- Establish secure device usage policies
- Create incident response and recovery frameworks
- Utilize automated threat detection algorithms
- Perform periodic penetration testing
Pro tip: Develop a dynamic security ecosystem that combines technological solutions with continuous human oversight and adaptive learning mechanisms.
Strengthen Your ERP Security with Singleclic’s Expert Solutions
Protecting your Enterprise Resource Planning system is more crucial than ever in today’s evolving cyber threat landscape. The article highlights critical challenges such as ransomware attacks, insider threats, and complex vulnerabilities that can disrupt your operations and compromise sensitive data. You need real-time threat detection, adaptive security architectures, and compliance with stringent healthcare and banking regulations to stay secure.
Singleclic understands these pressing needs with over 10 years of regional experience delivering advanced ERP & CRM Implementation and Business Process Automation solutions. We blend AI-driven cybersecurity measures, multi-factor authentication, and continuous monitoring to safeguard your ERP environment. Our tailored approach helps organizations in Saudi Arabia, UAE, and Egypt move beyond basic digitalization toward true operational optimization.
Take control of your ERP security today by partnering with Singleclic. Visit Singleclic now to discover how our scalable, cutting-edge technology and deep industry expertise can protect your business from emerging cyber risks. Don’t wait until a breach threatens your data integrity. Act now to secure your digital future.
Frequently Asked Questions
What are the key components of cybersecurity in modern ERP systems?
Key cybersecurity components for modern ERP systems include real-time threat monitoring, automated intrusion detection systems, advanced authentication protocols, continuous vulnerability assessment, encrypted data transmission channels, and granular access control mechanisms.
How do traditional ERP cybersecurity approaches differ from modern, AI-driven methods?
Traditional ERP cybersecurity approaches are often slower and reactive, limited to known attacks with high manual involvement. In contrast, modern AI-driven methods offer real-time, proactive detection that learns and adapts to new threats, requiring fewer manual resources.
What are the common threats targeting ERP systems?
Common threats targeting ERP systems include ransomware infiltration, insider threat exploitation, advanced persistent threats (APTs), unauthorized data access, credential theft, supply chain compromises, and complex malware injection.
What practical steps can organizations take to avoid system vulnerabilities in ERP environments?
Organizations can mitigate ERP vulnerabilities by conducting regular security assessments, implementing zero-trust architecture, developing comprehensive employee training programs, maintaining rigorous patch management, enabling advanced multi-factor authentication, and establishing incident response frameworks.









