TL;DR:
- Over 94% of enterprises faced cloud security incidents in 2025, mainly due to misconfigurations and identity misuse.
- Effective cloud security requires continuous management, proactive enforcement, and aligning with regional regulations.
- Adopting frameworks like zero trust, CIEM, and the shared responsibility model enhances resilience in multi-cloud environments.
Over 94% of enterprises experienced at least one cloud security incident in 2025, yet many organizations still operate under the assumption that their cloud provider handles security end-to-end. For C-level executives and IT leaders scaling operations across KSA and UAE, that assumption is not just wrong. It is expensive. This guide cuts through the noise to give you a grounded understanding of today’s cloud threat landscape, the frameworks that actually work, and the specific actions your organization needs to take to build genuine, lasting resilience.
Table of Contents
- The evolving cloud threat landscape
- Hidden risks: Where cloud security efforts fail
- Core frameworks: Modern approaches to cloud security
- Strategic priorities: Securing your cloud ecosystem in practice
- Perspective: The misunderstood drivers of true cloud resilience
- Next steps: Secure your digital journey with tailored expertise
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Incidents are common | Most enterprises face cloud breaches each year, making proactive security a must. |
| Human error is critical | Misconfigurations and identity mismanagement are the top causes of cloud incidents. |
| Modern frameworks required | Zero trust, CIEM, and robust controls address unique cloud risks. |
| Continuous action wins | Real-time monitoring and agentic enforcement provide true resilience, not just compliance. |
| Leadership drives results | Executive focus and organizational alignment are essential for lasting cloud security. |
The evolving cloud threat landscape
Cloud adoption across KSA and UAE has moved well past the experimental stage. Government-mandated digital transformation programs, Vision 2030 in Saudi Arabia, and the UAE’s national AI strategy have pushed enterprise workloads to the cloud at an accelerating pace. Most large organizations in the region now run hybrid or multi-cloud environments spanning multiple providers. That ubiquity creates an enormous and growing attack surface.
The data reflects this clearly. 48% of cyberattacks target cloud environments, and misconfigurations alone caused 45% of cloud breaches recorded in recent years. These are not sophisticated zero-day exploits. They are preventable mistakes in how cloud resources are set up, maintained, and monitored. That distinction matters for your board conversations, because it shifts the narrative from “inevitable risk” to “addressable operational failure.”
“Cloud security is no longer an IT concern. It is a business continuity concern. Every misconfiguration is a potential headline, a regulatory penalty, and a customer trust issue.” — Tamer Badr, Singleclic
Understanding this as a cloud security business necessity means recognizing that the threat vectors have changed. Attackers are no longer just targeting perimeter networks. They are exploiting public-facing APIs, unused storage buckets with exposed credentials, and over-privileged service accounts that nobody has reviewed in months. Once inside, lateral movement through interconnected cloud services can be devastatingly fast and difficult to detect.
| Threat vector | Share of incidents | Primary cause |
|---|---|---|
| Misconfiguration | 45% | Human error, lack of review |
| Identity and access abuse | 38% | Excess privileges, stolen credentials |
| Public-facing asset exploitation | 30% | Unpatched services, exposed APIs |
| Supply chain compromise | 19% | Third-party integrations, CI/CD pipelines |
| Insider threats | 14% | Lack of monitoring, entitlement drift |
For regional enterprises, the stakes are compounded by sector-specific regulations. Healthcare entities operating under UAE MOHAP guidelines, financial institutions subject to Saudi SAMA cybersecurity frameworks, and government contractors under NCA requirements all face heightened compliance obligations alongside these technical realities. Reviewing cloud security for IT leaders in KSA and UAE reveals just how deeply these regulatory layers intersect with your technical posture.
Hidden risks: Where cloud security efforts fail
You may already have a cloud security tool in place. You may even have a dedicated team. Yet the evidence suggests that investment alone is not closing the gap. The problems tend to be structural, not budgetary.
The most striking finding from recent research is the sheer volume of unaddressed exposure per cloud asset. The average cloud asset carries 115 vulnerabilities, with 61% of confirmed cloud compromises being identity-related. That means for every workload you run, there are likely dozens of unpatched issues sitting below the surface, waiting to be chained together into an attack path. Most of those vulnerabilities are not individually critical. But attackers do not need a single catastrophic flaw. They need a sequence of small ones.
Here are the most common failure points we observe across enterprise environments in the region:
- Non-human identities left unchecked. Service accounts, automation scripts, CI/CD pipeline credentials, and API keys often carry permissions set during initial deployment and never reviewed again. These accounts accumulate excessive privileges quietly.
- Multi-cloud visibility gaps. When your data and workloads span AWS, Azure, and Google Cloud simultaneously, no single native tool gives you a complete picture. Attackers exploit the gaps between these silos.
- Ephemeral resource risks. Containers and serverless functions spin up and disappear in minutes. Traditional security scanning tools miss them entirely because they are gone before a scan completes.
- Shadow IT and untracked assets. Teams spin up resources outside formal procurement processes. These assets rarely appear in your asset inventory, which means they are never patched, never monitored, and perfectly positioned as entry points.
- Alert fatigue masking real threats. Organizations running legacy security tools generate thousands of low-priority alerts daily. Real threats get buried in noise. Security teams triage for hours only to miss the one alert that mattered.
Pro Tip: Conduct a quarterly entitlement review focused specifically on non-human identities. Service accounts and API keys are the most overlooked attack surface in cloud environments, and reducing their permissions to the minimum required for each function can cut your identity-related risk dramatically.
Addressing the common mistakes in cloud data protection that enterprises make requires more than buying another tool. It requires an honest inventory of what you own, what permissions exist across that inventory, and whether your monitoring actually covers everything in scope. Building information protection in cloud into your architecture from the design phase, rather than bolting it on afterward, is the difference between security that scales and security that cracks under pressure.
Core frameworks: Modern approaches to cloud security
With the risks clearly mapped, the next step is selecting the right frameworks and tools to address them systematically. Several proven models have emerged as the foundation of mature cloud security programs, and understanding how they complement each other is critical for IT leaders building or refreshing their strategy.
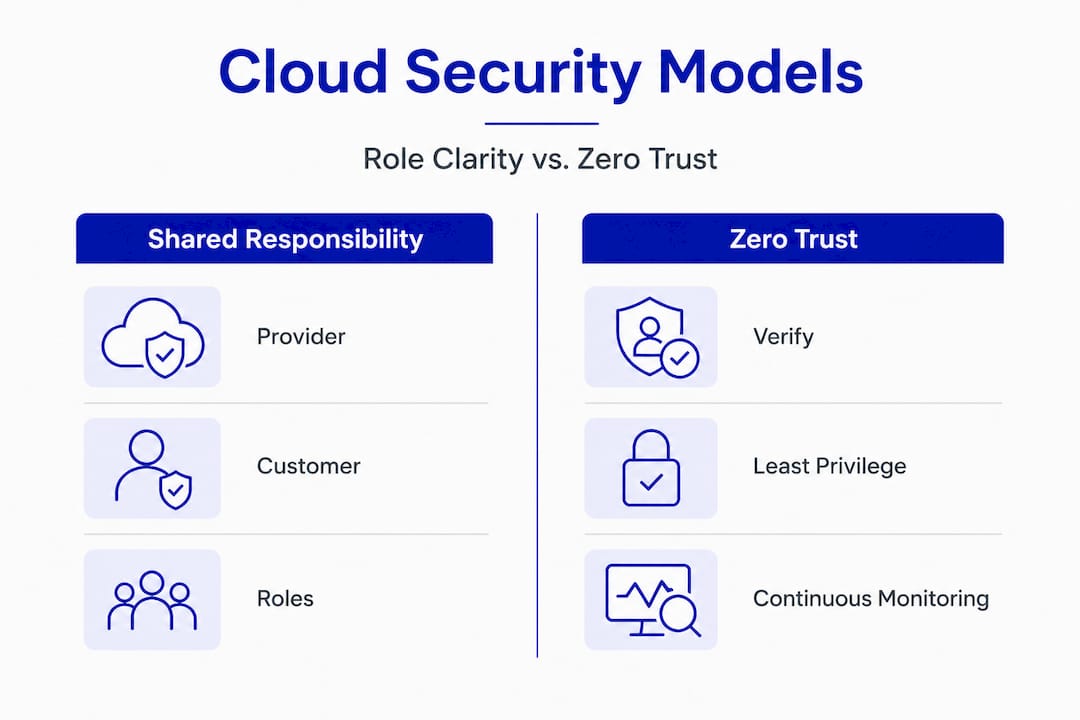
1. The shared responsibility model
This is the most foundational concept in cloud security and the most frequently misunderstood. The shared responsibility model is clear: your cloud service provider secures the underlying infrastructure, including physical data centers, networking hardware, and the hypervisor layer. Everything above that, including your data, your configurations, your access controls, and your applications, is your responsibility. Many breaches happen precisely because organizations assume their provider covers more than it does.
2. Zero trust architecture
Zero trust operates on a simple but powerful principle: trust nothing, verify everything. No user, device, or service is automatically trusted, even if it is inside your network perimeter. Every access request is authenticated, authorized, and continuously validated. For enterprises in KSA and UAE operating across multiple locations and with remote workforces, zero trust is not optional. It is the architecture that makes distributed work safe.
3. Cloud infrastructure entitlement management (CIEM)
CIEM tools specialize in discovering and right-sizing permissions across cloud environments. They map every identity, human and non-human, to its actual permissions and compare that to what it actually needs to function. Excess permissions are flagged and remediated automatically or with guided workflows. This directly addresses the identity-related risk that drives the majority of confirmed compromises.
4. AI-enabled risk detection and attack path analysis
Modern cloud security platforms use machine learning to correlate signals across your environment and surface attack paths before they are exploited. Rather than alerting on individual events, these systems identify chains of low-severity findings that together represent a high-risk path to a critical asset.
5. CSA Cloud Controls Matrix (CCM) v4.1
The CSA CCM v4.1 is the most widely adopted cloud-specific control framework globally. Its latest version adds controls specifically designed for edge computing environments and strengthens resilience requirements across domains including identity management, encryption, incident response, and supply chain security. For enterprises seeking a structured way to measure and improve their cloud security posture, the CCM provides both a benchmark and a roadmap.
| Framework | Primary focus | Best suited for |
|---|---|---|
| Shared responsibility model | Role clarity between provider and customer | All cloud users |
| Zero trust architecture | Access control and lateral movement prevention | Distributed, multi-location enterprises |
| CIEM | Identity and permission management | Multi-cloud, complex IAM environments |
| AI-driven risk platforms | Attack path correlation and prioritization | Large-scale environments with high alert volume |
| CSA CCM v4.1 | Control benchmarking and compliance | Regulated industries, compliance-driven enterprises |
Reviewing best practices for cloud security alongside an understanding of on-premise vs cloud security tradeoffs helps leaders make more informed architectural decisions rather than defaulting to whichever solution a vendor presents first.
Strategic priorities: Securing your cloud ecosystem in practice
Frameworks are only useful when they translate into concrete action. For executives and IT leaders in KSA and UAE, the following priorities reflect both global best practices and the specific regulatory, operational, and cultural context of the region.
Move from passive monitoring to proactive enforcement. Most organizations today monitor their cloud environments and generate alerts. Fewer act on those alerts consistently. Only 17% of firms have deployed CIEM, and organizations that prioritize CIEM alongside zero trust reduce their mean time to detect (MTTD) from an industry average of 143 days to dramatically lower timeframes. That 143-day window is not an abstract statistic. It represents months during which an attacker may have established persistence, exfiltrated data, and pivoted to additional systems.
Close IAM gaps with urgency. Identity and access management (IAM) is where most cloud security programs have their deepest gaps. Review every service account, every API key, and every role assignment. Remove permissions that are not actively required. Implement just-in-time access for privileged operations so that elevated permissions exist only for the duration of a specific task, then are automatically revoked.
- Establish real-time visibility across all cloud assets, including containers, serverless functions, and shadow IT resources. If it is not in your asset inventory, it is not being protected.
- Build and regularly test an incident response plan specific to cloud environments. Generic IT incident response plans do not account for the speed, scale, and cross-cloud complexity of modern cloud attacks.
- Address supply chain and third-party risk by reviewing the permissions and access patterns of every integrated vendor and tool. In KSA and UAE, where government and financial sector supply chains are particularly complex, this is especially critical.
- Align your security posture with regional regulatory requirements. SAMA’s cybersecurity framework, NCA’s essential cybersecurity controls, and UAE NESA standards all have specific cloud-related requirements that go beyond generic international frameworks.
Pro Tip: Set a specific board-level metric around MTTD and mean time to respond (MTTR). When security performance is tied to executive dashboards rather than buried in technical reports, it drives the cross-functional accountability that actually reduces risk.
Securing data in multi-cloud environments requires a governance model that spans every provider, every region, and every team. Pairing that with cloud security compliance solutions ensures that your technical controls and your regulatory obligations stay aligned as your environment grows.
Perspective: The misunderstood drivers of true cloud resilience
Here is what most cloud security conversations miss: throwing budget at point-in-time tools does not build resilience. It builds the appearance of security. And those two things are very different when a breach actually occurs.

In our experience working with enterprises across KSA, UAE, and Egypt, the organizations that achieve genuine cloud resilience share three characteristics that have nothing to do with which security vendor they chose. First, they treat identity governance as a continuous operational discipline, not an annual audit. Second, their security leadership has direct access to the CEO and board, not just the CTO. Third, their security culture extends beyond the IT department to include developers, finance teams, and procurement, because those are the people spinning up cloud resources and signing vendor contracts.
Proactive, agentic enforcement rather than point-in-time monitoring is what separates resilient organizations from reactive ones. Agentic AI-driven systems do not wait for a human to review a report and decide to act. They correlate signals, identify risk paths, and enforce controls in real time. That capability is increasingly accessible and should be a priority investment for any enterprise running workloads at scale.
The uncomfortable truth is that most cloud security failures are organizational before they are technical. A misconfiguration that exposes customer data is usually a symptom of a culture where security reviews are seen as slowing down deployment, not protecting the business. Changing that culture requires executive mandate, not just security team advocacy.
Understanding where cloud fits in your digital transformation strategy means accepting that security is not a layer you add at the end. It is a design principle that shapes every architecture decision, every vendor relationship, and every team’s operating norms. The organizations that get this right do not just avoid breaches. They build environments that are genuinely faster, more reliable, and more trustworthy than their competitors.
Next steps: Secure your digital journey with tailored expertise
Turning this clarity into action requires more than a checklist. It requires a partner who understands the specific regulatory landscape, operational realities, and technology ecosystems that enterprises in KSA and UAE navigate every day.
At Singleclic, we combine 10 years of regional delivery experience with deep expertise in enterprise AI, business process automation for leaders, and compliance-aligned transformation programs. Our team of 70 consultants and engineers has worked with organizations including Emirates Health Services, QNB, and Emaar Misr to build cloud environments that are both high-performing and genuinely secure. Whether you need a cloud security assessment, a zero trust architecture roadmap, or robotic process automation solutions that reduce manual risk exposure, we bring the experience and regional context to deliver results. Reach out to start a conversation about what cloud resilience looks like for your organization specifically.
Frequently asked questions
What is the biggest risk to cloud security for enterprises?
Misconfigurations cause 45% of breaches while 61% of compromises are identity-related, making these two areas the most critical and most neglected in enterprise cloud security programs.
How does cloud security improve business resilience?
Strong cloud security reduces the probability and impact of breaches, which average $4.35M in total cost when they occur. Faster detection and containment directly protect revenue, customer trust, and regulatory standing.
Which cloud security frameworks are most relevant in 2026?
Zero trust architecture, CIEM, the shared responsibility model, and the CSA CCM v4.1 are the leading frameworks for organizations building mature, resilient cloud security programs in 2026.
Are AI and automation helping or hurting cloud security?
Both. AI workloads expand the attack surface through model endpoints and APIs, but agentic AI enables proactive enforcement and real-time risk correlation that far outpaces what human teams can achieve alone.
What is the shared responsibility model in cloud security?
The shared responsibility model means your cloud provider secures the underlying infrastructure, while your organization remains fully responsible for data protection, configuration management, and identity and access controls.









